Security & Networking
When the Hunter Becomes
the Hunted: Inside the Beast
Ransomware Operator’s Exposed Toolkit
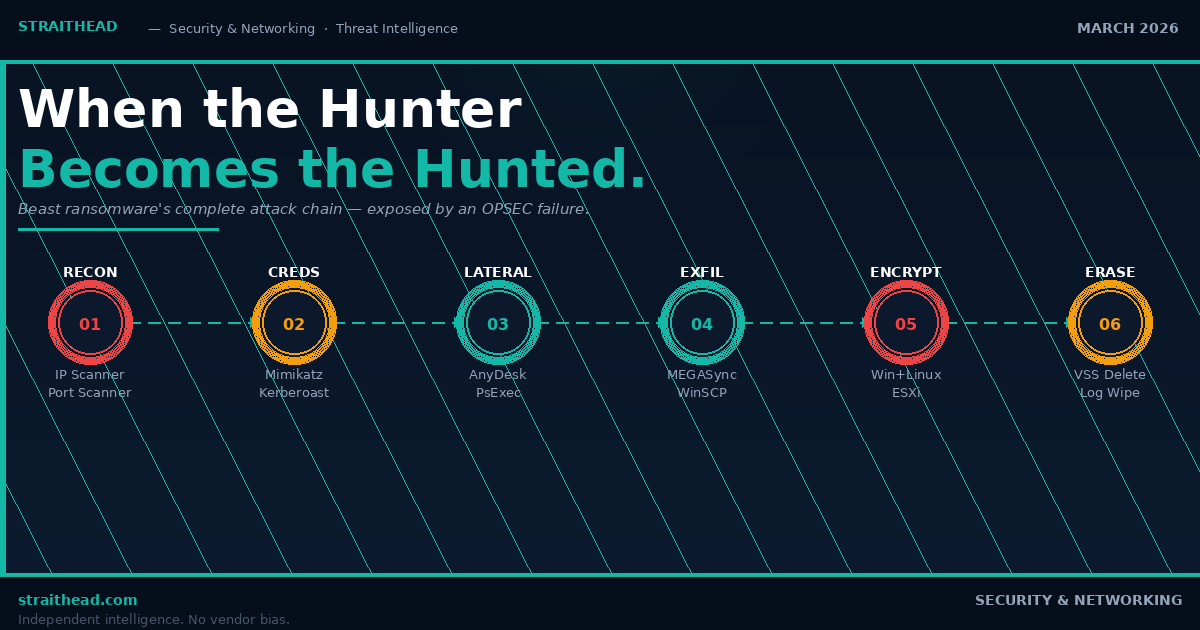
A catastrophic operational security failure by a Beast ransomware affiliate laid bare the group’s complete attack arsenal on an open German cloud server — gifting threat researchers an unprecedented view of the modern ransomware kill chain, from first reconnaissance to forensic erasure.
Ransomware operators are meticulous architects of digital destruction — until they are not. In March 2026, a member of the Beast ransomware group left the front door of their operational server wide open, exposing the group’s entire attack compendium to anyone with the wherewithal to look. Threat intelligence firm Team Cymru found it first. What they uncovered is not merely the tradecraft of a single affiliate — it is a mirror held up to the entire ransomware-as-a-service ecosystem.
The discovery originated from Team Cymru’s passive internet telemetry collection — specifically, its NetFlow-augmented Open Ports detection system, which identified a directory listing running on port 8000 at IP address 5.78.84[.]144, hosted on AS212317 — a German cloud provider. The file names alone were sufficient to reconstruct the operator’s complete methodology. What followed was a forensic dissection of a ransomware kill chain that proceeds with the precision and brutality of a surgical offensive operation.
Beast ransomware is a Ransomware-as-a-Service platform that emerged in June 2024, first advertised on the underground forum RAMP — the same marketplace that incubated its predecessor, Monster ransomware. It operates on a double-extortion model: data is exfiltrated before encryption, and victims who decline to pay face publication of their stolen records on BEAST LEAKS, the group’s dedicated Tor-hosted data leak site. Operations paused in November 2025 and resumed aggressively in January 2026, with multiple victims posted throughout February and March.
The Beast Attack Chain — Six Phases from Intrusion to Erasure
Advanced Port Scanner
Everything.exe
FolderSize-x64
LaZagne
Automim
enable_dump_pass.reg
Kerberos.ps1
PsExec
OpenSSH
for Windows
WinSCP
Klink (SFTP)
encrypter-linux-x64.run
(VMware ESXi)
(VSS deletion)
CleanExit.exe
(log wipe)
Reconnaissance: Mapping the Terrain Before the Assault
Every sophisticated intrusion begins not with malware, but with intelligence gathering — a phase indistinguishable, at the network layer, from routine administrative activity. The Beast operator’s toolkit reveals a disciplined approach to pre-attack reconnaissance that prioritises efficiency and stealth in equal measure.
The server contained copies of Advanced IP Scanner and Advanced Port Scanner — legitimate network administration tools routinely abused to enumerate internal hosts, map open RDP and SMB ports, and identify high-value targets within a compromised network perimeter. Alongside these, Everything.exe — a lightning-fast file indexing engine — was present, enabling the operator to locate sensitive documents, credential stores, and backup configurations with a speed that manual directory traversal could never match. Perhaps most revealing was FolderSize-x64: a utility that identifies which servers contain the largest data volumes, allowing the operator to triage encryption targets by potential ransom leverage before a single file is touched.
Defender Implication
The presence of network scanning tools in a production environment — particularly Advanced IP Scanner and Advanced Port Scanner — should trigger immediate investigation. These are not tools that legitimate administrators run without a documented change request. Their appearance in endpoint telemetry or network traffic logs is a high-confidence indicator of active pre-ransomware reconnaissance activity.
Credential Harvesting: The Keys to the Kingdom
Domain administrator credentials are the ransomware operator’s most coveted prize — the master key that transforms a foothold into total network ownership. The Beast operator’s credential-harvesting arsenal is comprehensive, multi-layered, and entirely consistent with the tooling used by the most prolific ransomware groups operating today.
The server contained Mimikatz, LaZagne, and Automim — the triumvirate of post-exploitation credential dumping. Mimikatz extracts plaintext passwords and NTLM hashes directly from the Windows LSASS process memory. LaZagne systematically recovers stored credentials from browsers, email clients, databases, and system password managers. Automim automates the Mimikatz workflow for environments where speed or stealth requirements demand it.
Two tools in this phase deserve particular attention. The first is enable_dump_pass.reg — a Windows registry modification file that re-enables WDigest authentication, forcing Windows to store user credentials in cleartext in memory. This technique, which Microsoft disabled by default in Windows 8.1 and Server 2012 R2, exists precisely because many enterprise environments still run legacy systems or configurations that make this re-enablement viable. Once applied, Mimikatz can harvest plaintext credentials without requiring any hash-cracking overhead. The second is Kerberos.ps1 — a PowerShell implementation of Kerberoasting, the technique whereby service account Ticket Granting Service (TGS) tickets are requested from Active Directory and subsequently cracked offline. Service accounts with weak passwords and excessive privileges remain endemic in enterprise environments, making Kerberoasting a reliable path to lateral movement even against hardened targets.
“The way that a lot of ransomware groups operate is, they’re reusing a lot of the tools that other ransomware groups use. For many companies, it is not as hard as it seems to actually defend against these attacks — because as long as you have the right protections in place to block these tools from being able to run on your systems, they’re not going to be able to hit you.”
Will Thomas, Senior Threat Intelligence Advisor, Team Cymru — Dark Reading, March 2026Lateral Movement: Becoming the Network
With credentials secured, the Beast operator moves to colonise the network — propagating from the initial beachhead to every accessible system before triggering the final destructive payload. The elegance of this phase lies in its paradox: the tools used are not malicious. They are, in most environments, trusted.
AnyDesk — the legitimate remote monitoring and management tool used by IT support teams worldwide — was present on the server. Its value to ransomware operators is not despite its legitimacy but because of it. Endpoint Detection and Response systems, by default, do not flag AnyDesk as malicious. Once installed on a compromised machine, it provides persistent, encrypted remote access that survives reboots, resists removal, and generates no meaningful security alert in most enterprise environments. The same AnyDesk application was found in the toolkits of Qilin and Akira — two of the most prolific ransomware operations currently active.
Complementing AnyDesk are PsExec — Microsoft’s own Sysinternals tool for remote command execution — and OpenSSH for Windows, which enables the creation of encrypted SSH tunnels for remote access across network segments that might otherwise be partitioned from the attacker’s infrastructure. Together, these tools allow an operator with valid domain credentials to move through an enterprise network with the same apparent authority as a systems administrator.
Exfiltration: The Silent Extraction
Before encryption renders the victim’s data inaccessible — and therefore valueless as leverage — the Beast operator systematically extracts it. This is the double-extortion foundation: the threat to publish stolen data on BEAST LEAKS creates an independent coercive pressure that persists even if the victim successfully restores from backup.
The exfiltration toolkit centres on MEGASync — the desktop synchronisation client for Mega.nz, the cloud storage platform. MEGASync’s architecture is well-suited to large-scale data exfiltration: it handles multi-gigabyte transfers with native compression, operates over standard HTTPS, and generates traffic that is indistinguishable from legitimate cloud backup activity in most network monitoring configurations. Additional exfiltration channels include WinSCP and Klink, providing SFTP-based transfer capabilities to operator-controlled infrastructure as redundant exfiltration paths.
Encryption: The Dual-Platform Kill
The Beast ransomware binary set reveals an architectural sophistication that elevates this group beyond opportunistic criminals. Two distinct encryption payloads were discovered on the server: encrypter-windows-cli-x86.exe and encrypter-linux-x64.run.
The Linux binary is the more strategically significant of the two. The explicit targeting of VMware ESXi hypervisors through a Linux encryptor represents the single most impactful evolution in enterprise ransomware architecture over the past three years. A VMware ESXi host is not merely a server — it is the physical substrate upon which an organisation’s entire virtualised infrastructure runs. A single ESXi host may support dozens of virtual machines: application servers, database instances, domain controllers, backup systems. Encrypting the hypervisor renders every guest machine simultaneously inaccessible. Recovery requires not the restoration of individual systems but the reconstruction of an entire virtualised environment — a process measured in days or weeks, not hours.
This dual-platform capability — Windows workstations and Linux hypervisors — ensures that a single Beast affiliate can achieve total network impact across heterogeneous enterprise environments. Beast also explicitly avoids encrypting devices located in Commonwealth of Independent States countries, including Russia, Belarus, and Moldova — a geographic exclusion that is functionally diagnostic of the group’s likely operational base.
| Tool | Phase | Function | Legitimacy |
|---|---|---|---|
| Advanced IP Scanner | Reconnaissance | Network host enumeration, RDP/SMB port mapping | Dual-use |
| Everything.exe | Reconnaissance | Fast file location and sensitive data discovery | Dual-use |
| Mimikatz | Credential Theft | LSASS memory dump, NTLM hash extraction | Malicious |
| enable_dump_pass.reg | Credential Theft | Re-enables WDigest to store credentials in cleartext | Malicious |
| Kerberos.ps1 | Credential Theft | Kerberoasting — offline TGS ticket cracking | Malicious |
| AnyDesk | Lateral Movement | Persistent remote access, EDR-evasive | Dual-use |
| PsExec | Lateral Movement | Remote command execution across domain | Dual-use |
| MEGASync | Exfiltration | Large-volume data upload to Mega.nz | Dual-use |
| disable_backup.bat | Pre-Encryption | Deletes Volume Shadow Copies, disables VSS | Malicious |
| encrypter-linux-x64.run | Encryption | Linux / VMware ESXi ransomware payload | Malicious |
| CleanExit.exe | Forensic Erasure | Log wipe and tooling removal post-encryption | Malicious |
The Final Act: Destroying the Safety Net
The most operationally decisive element of the Beast operator’s toolkit is not the ransomware binary. It is disable_backup.bat — a batch script whose function is elegantly brutal: it enumerates and deletes every Windows Volume Shadow Copy, disables the Volume Shadow Copy Service entirely, and halts any running backup processes. This single script, executed before the encryption payload deploys, eliminates the most common recovery path available to enterprise victims.
Volume Shadow Copies are Windows’ native point-in-time filesystem snapshots — the backup mechanism that allows administrators to restore individual files or entire system states without deploying dedicated backup software. Their destruction is not an afterthought in modern ransomware operations. It is the first priority of the pre-encryption phase, because a victim who can restore from shadow copies has no need to pay a ransom. The script specifically targets VSS because it is ubiquitous, often unmonitored, and its deletion — absent specific security tooling — generates no alert in a default Windows environment.
Network-attached backups and replication targets fare no better unless they are designed for air-gap or immutability. As Team Cymru’s Will Thomas noted, backup systems that replicate sensitive data — Active Directory, server images, database snapshots — to an online storage target are accessible to an attacker with domain administrator credentials. The delete command is a single line. The recovery timeline is weeks.
After encryption, CleanExit.exe executes the final act: wiping operator tooling from the compromised environment and clearing event logs, degrading the forensic trail available to incident responders and substantially impeding post-incident attribution.
Critical Finding
The presence of disable_backup.bat on Beast’s server confirms what threat intelligence has long asserted: backup destruction is not incidental to ransomware operations — it is doctrinal. Any backup strategy that does not account for the deliberate, targeted deletion of shadow copies and online backup targets by a domain-privileged adversary is not a ransomware recovery strategy. It is a false sense of security.
What Beast’s Toolkit Reveals About the Entire RaaS Ecosystem
The most strategically significant revelation from Team Cymru’s analysis is not what is unique about Beast’s toolkit. It is what is not unique. Every tool in Beast’s arsenal — Mimikatz, AnyDesk, PsExec, MEGASync, the VSS deletion script — appears in the known toolkits of Qilin, Akira, BlackLock, and the broader constellation of active ransomware-as-a-service operations. All of them are catalogued in the open-source Ransomware Tool Matrix maintained by the security research community.
This convergence is not coincidental. It is the structural consequence of the RaaS model itself. Ransomware-as-a-service platforms provide affiliates — the operators who conduct the actual intrusions — with core encryption binaries and infrastructure. The surrounding toolkit is sourced independently, drawn from a shared ecosystem of dual-use tools, publicly available credential dumpers, and purpose-built utilities that have proven effective across hundreds of campaigns. The result is a tactical homogeneity across the ransomware threat landscape that has profound defensive implications.
“As long as you have the right protections in place to block these tools from being able to run on your systems, they’re not going to be able to hit you.”
Will Thomas, Senior Threat Intelligence Advisor, Team CymruThomas’s observation is both reassuring and demanding. Reassuring because the homogeneity of ransomware tooling means that a well-configured defensive programme targeting the known dual-use tool set provides disproportionate protection across the threat landscape — not just against Beast, but against every group that relies on the same instruments. Demanding because that configuration requires deliberate, sustained investment in detection engineering, application control, and backup architecture that most enterprises have not yet made.
Five Defensive Imperatives Every Enterprise Should Act On Now
The Beast operator’s OPSEC failure has delivered the security community a gift of extraordinary intelligence value. The appropriate response is not satisfaction at the adversary’s error — it is a rigorous audit of defensive posture against the attack chain it revealed.
1. Treat dual-use tools as threat indicators, not safe exceptions. Advanced IP Scanner, AnyDesk, PsExec, and MEGASync are legitimate in the right context — and unambiguous intrusion signals in the wrong one. Application control policies and network traffic monitoring should flag their unexpected appearance as high-severity events requiring immediate investigation.
2. Harden WDigest and service account Kerberos exposure. Confirm WDigest is disabled via Group Policy across all domain-joined systems. Audit service accounts with SPNs for password complexity and privilege scope. These two controls eliminate the primary credential-harvesting pathways exposed in Beast’s toolkit.
3. Architect backups for adversarial conditions, not routine failures. Immutable, air-gapped, or offline backups that cannot be reached by a domain administrator are the single most important ransomware recovery control. Verify that VSS deletion cannot eliminate your last line of defence. Test restoration under simulated adversarial conditions — not just hardware failure scenarios.
4. Extend detection coverage to VMware ESXi and Linux hosts. The presence of a Linux encryptor targeting ESXi hypervisors confirms that Windows-centric detection strategies leave critical infrastructure unmonitored. ESXi hosts require independent integrity monitoring, privileged access controls, and network segmentation from the domain environment.
5. Deploy against the Ransomware Tool Matrix proactively. Team Cymru’s analysis confirmed that Beast’s entire toolkit is catalogued in the open-source Ransomware Tool Matrix. This resource should be a mandatory input to your detection engineering backlog — not a reference consulted after an incident.
Sources & References
- Team Cymru — “The Beast Returns: Analysis of a Beast Ransomware Server”, March 2026: team-cymru.com
- Dark Reading — “Cyber OpSec Fail: Beast Gang Exposes Ransomware Server”, Robert Lemos, March 20 2026: darkreading.com
- OpenText Cybersecurity Community — “Beast Ransomware’s toolkit revealed by exposed directory”, Laura French, March 19 2026
- OffSeq Radar — “Beast Ransomware Toolkit: A Proactive Threat Intelligence Report”, March 20 2026
- News4Hackers — “Beast Ransomware’s Malicious Capabilities Exposed: Inside the Leaked Directory”, March 2026
- RansomLook — BEAST LEAKS Tor data leak site activity analysis, 2025–2026
- Ransomware Tool Matrix — Open source knowledge base of ransomware tooling: github.com/BushidoUK
- Purple Ops — “Ransomware Daily Report Q1 2026 Overview”, March 21 2026
- MITRE ATT&CK Framework — T1595, T1046, T1003, T1021, T1078, T1570, T1486
